See through attackers’ eyes.
Security testing that delivers fast, accurate and actionable security insights.
10,000+ security test cases.
A continuously updated library of attack vectors, vulnerability classes and misconfigurations.
Web App Testing
Broad security coverage for modern web applications, supporting every major framework and stack from server-rendered applications to single-page applications.
API Testing
Comprehensive security testing of modern APIs, supporting REST, GraphQL, and OpenAPI across every endpoint, parameter, and authentication mechanism.
What's under the hood.
Designed for continuous discovery, detailed remediation guidance and clear reporting.

Remediation Assistance
Every finding comes with context and clear guidance including recommended fixes and practical examples. No security degree required.

Authenticated Testing
Authenticated testing uses valid credentials to access protected areas, enabling deeper coverage across user-only functionality, business logic, and role-based access paths for more accurate and actionable findings.

Continuous Monitoring
Stay ahead of new vulnerabilities with automated daily testing. Continuous testing monitors your application for changes and emerging risks, ensuring new issues are detected as soon as they appear.
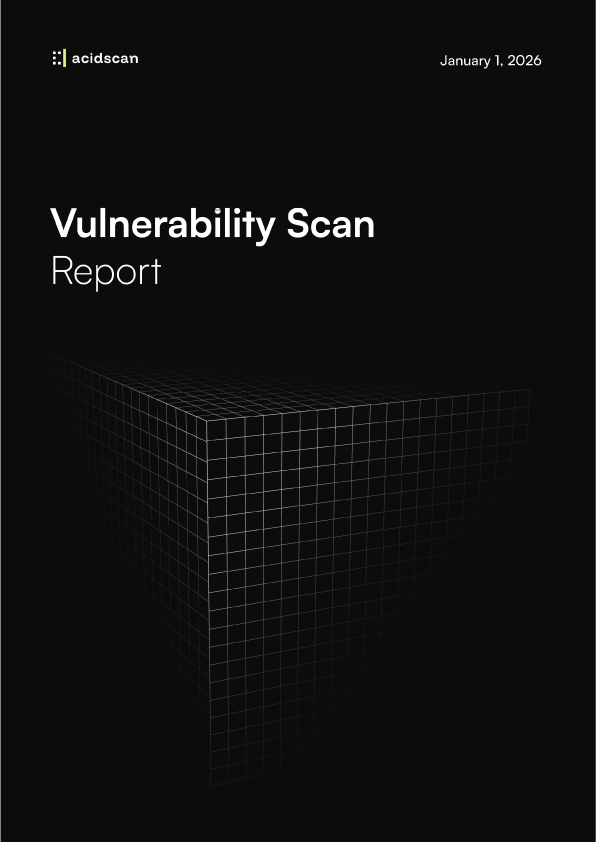
Audit-ready by default.
Clear, actionable reports and compliance-ready evidence for every stakeholder.
- Management-Focused Summary Reports
- Technical Deep-dive Reports
- Structured Data Reports
Point & Evalute.
Get started in minutes with our streamlined security testing workflow.
Add Your Asset
Simply specify the assets you want to test, and you'll be ready to start in minutes.
Run Assessment
Our advanced platform identifies vulnerabilities, misconfigurations, and security gaps.
Review Results
Receive prioritized findings with clear remediation guidance to strengthen your security.
How secure is your application, really?
Run a comprehensive assessment and find out before attackers do.
Get Started
